Understand and Manage Authorization Scopes in Google Apps Script
If you ever used Google Apps Script or add-ons for Google Drive/Docs/Sheets, let alone developed them, you have engaged with authorization scopes, whether you’re familiar with the term or not. For instance, the first time you run a new script you have to grant it specific permissions:
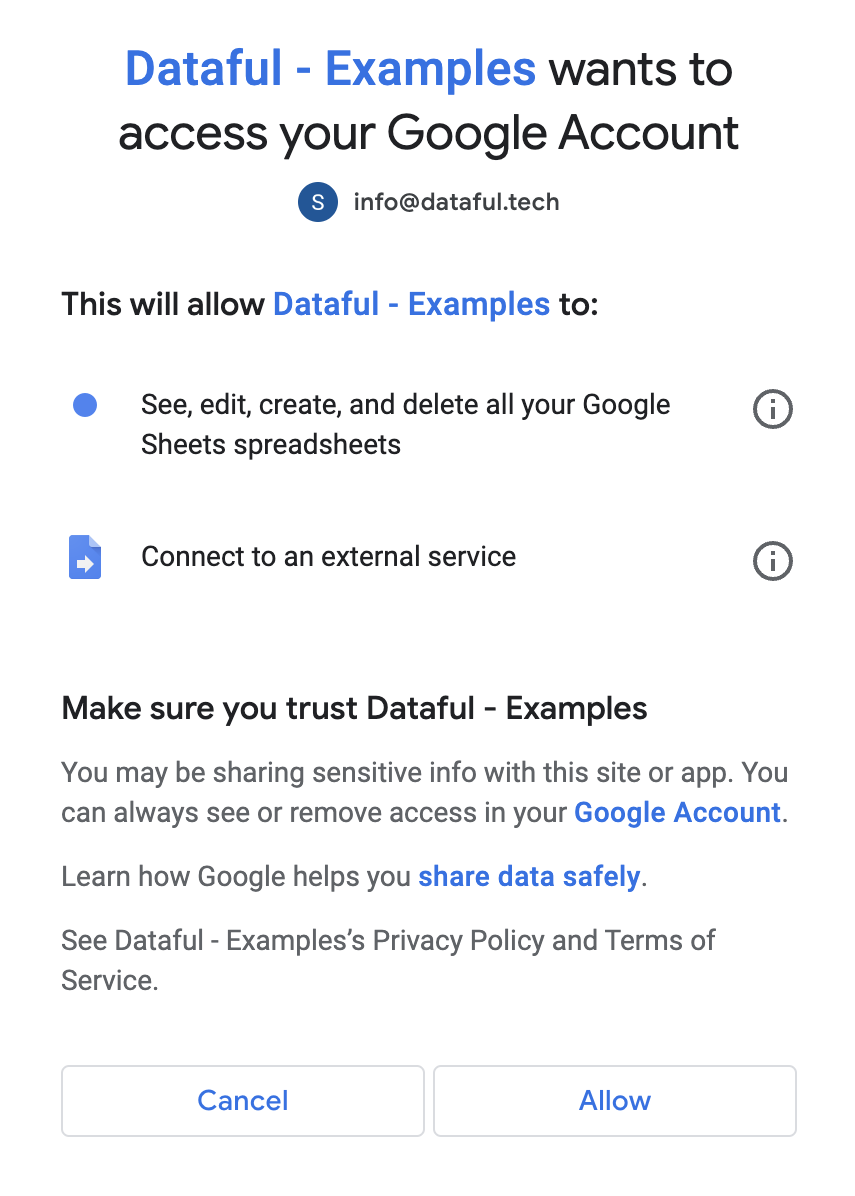
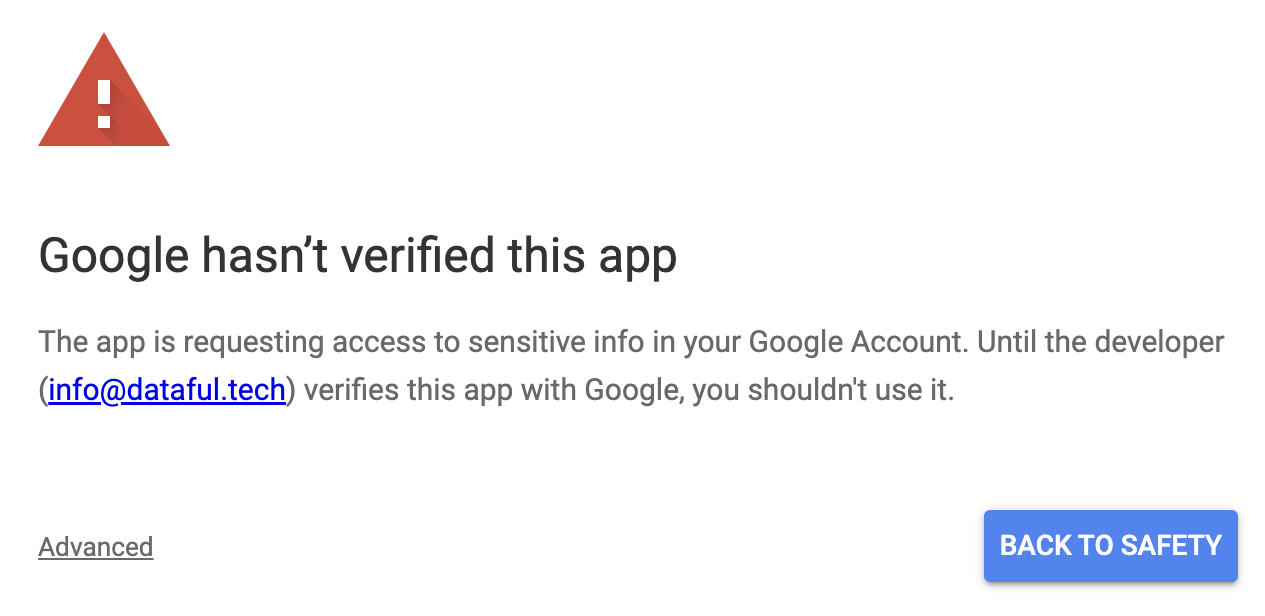
Sometimes you may even need to ignore Google’s security warnings indicating the potential risks associated with running a script:
In this article, we’ll delve into understanding what authorization scopes are, their importance, and how to audit and revoke them. This information is particularly crucial if you frequently use scripts: you might wish to revoke permissions that are no longer relevant. In another post we will see how to properly set scopes a script needs.
Understanding Authorization Scopes and Their Importance
Authorization scopes define what a script can do on your behalf concerning your data and account on Google. Security is the primary reason to be concerned about them. To illustrate, let’s compare two different scopes:
-
“See, edit, create, and delete all your Google Sheets spreadsheets” (scope
https://www.googleapis.com/auth/spreadsheets) – This allows the script full access to all spreadsheets you can access. Any action it performs is as though you did it yourself, including creating, reading, modifying, or deleting anything.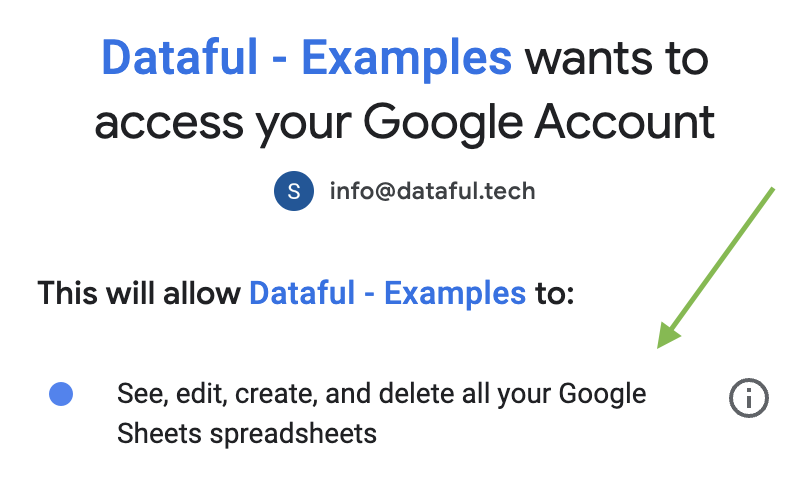
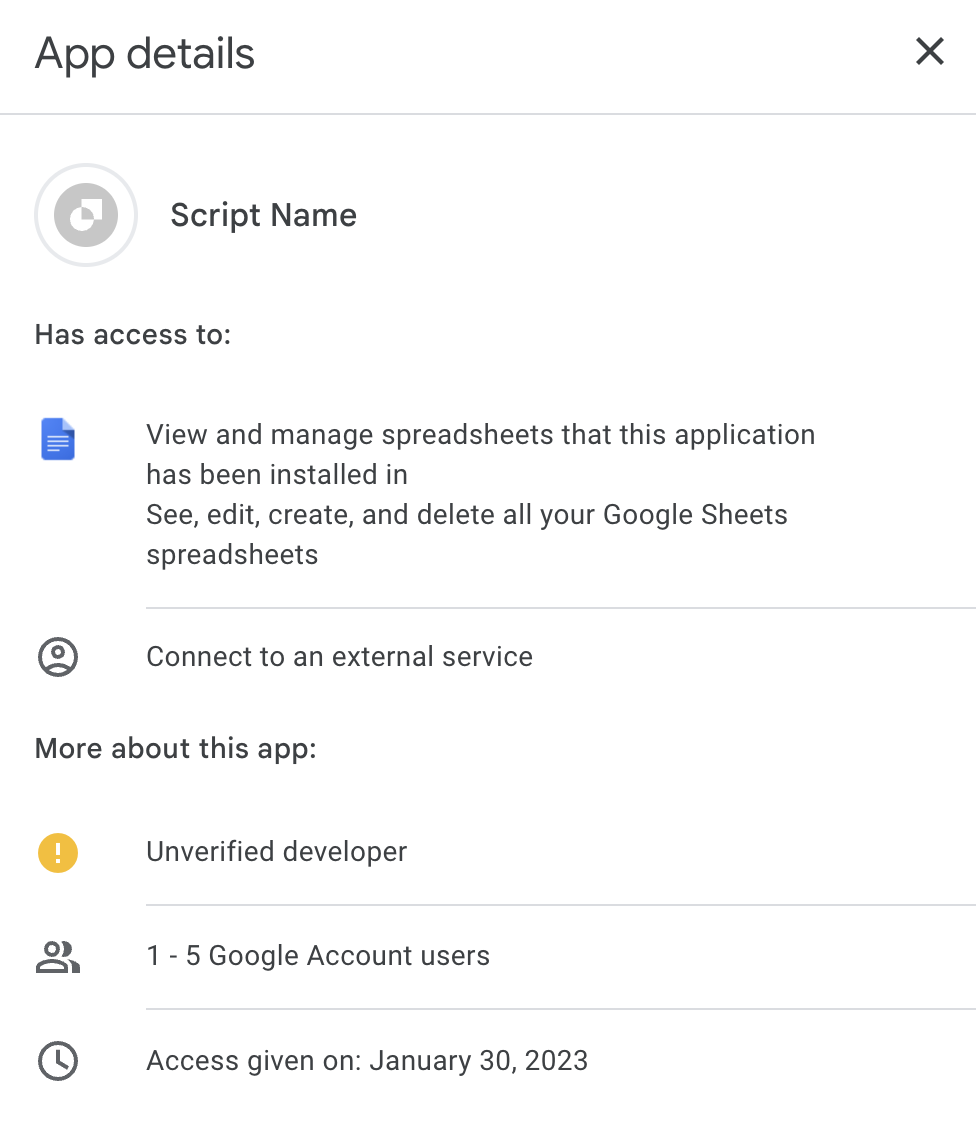
App asking for full access to all your spreadsheets -
“View and manage spreadsheets that this application has been installed in” (scope
https://www.googleapis.com/auth/spreadsheets.currentonly) – The script will only have access to the document where it was installed.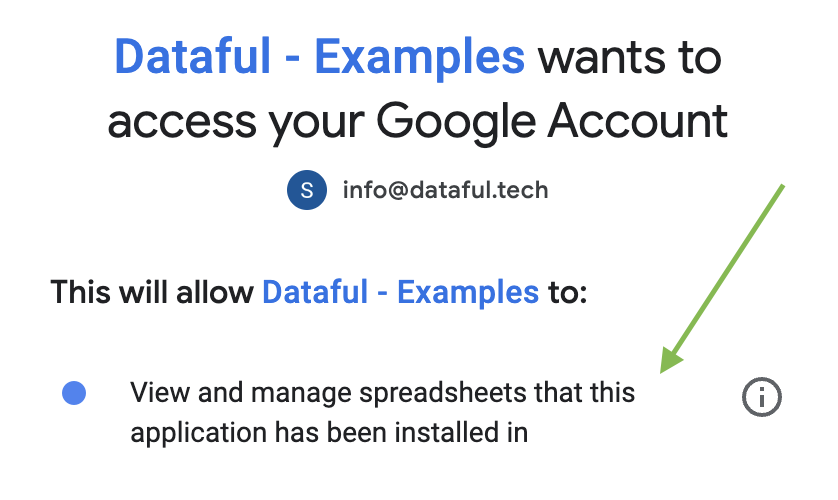
App asking for access only to the spreadsheet where it is installed
If you work alone and don’t share your documents and scripts with anyone, the distinction might not seem significant, and it may seem reasonable to grant broader permissions. However, even in this scenario, it’s advisable to use a more restrictive scope.
Suppose you shared a spreadsheet that includes an attached script with another editor. The script is also shared, and the editor can modify it, possibly to copy data or entire documents when you execute the script. Furthermore, if the script is set to run automatically (e.g., periodically via a time trigger), it could execute under your name unexpectedly.
Such instances can lead to data leaks and losses, with potential business and legal implications. A compromised account is all it takes for a security breach, and with the rise of cybercrime, it’s essential to stay vigilant and minimize risks early on.
Another challenging aspect of scopes is that it’s not straightforward to view the permissions you’ve granted and revoke them. We’ll explore the different options in the following section.
Auditing and Revoking Scopes
Several tools allow you to see the permissions you’ve granted and potentially detect any unusual activities. Google continually enhances these mechanisms, so the actual details may differ slightly from you we will see below.
Security Checkup
In your account’s Security section, you can find the Security Checkup. This tool highlights potential issues, such as scripts from unverified developers or scripts with dangerously permissive authorization scopes.
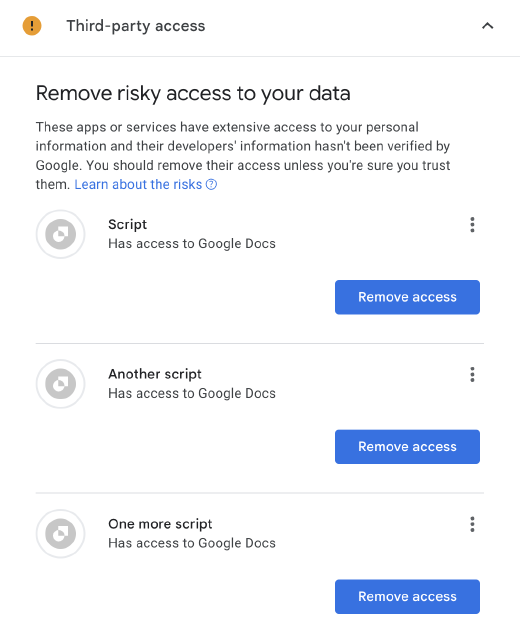
Here you can see the permissions you’ve granted to a given script:
Third-party Apps & Services
Again in the Security section, you can find Third-party apps & services. It is similar to the Security Checkup, lets you filter by permission type or application (script) name:
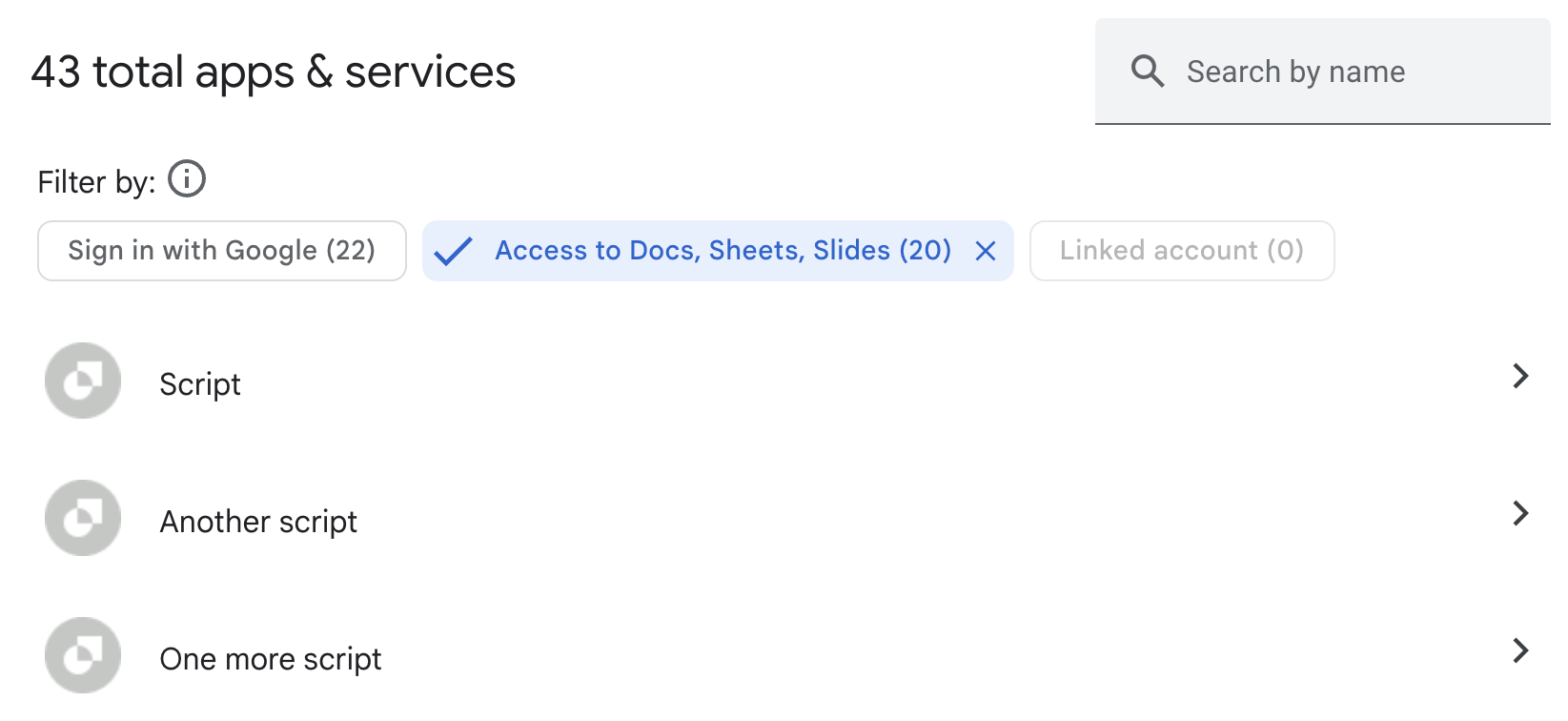
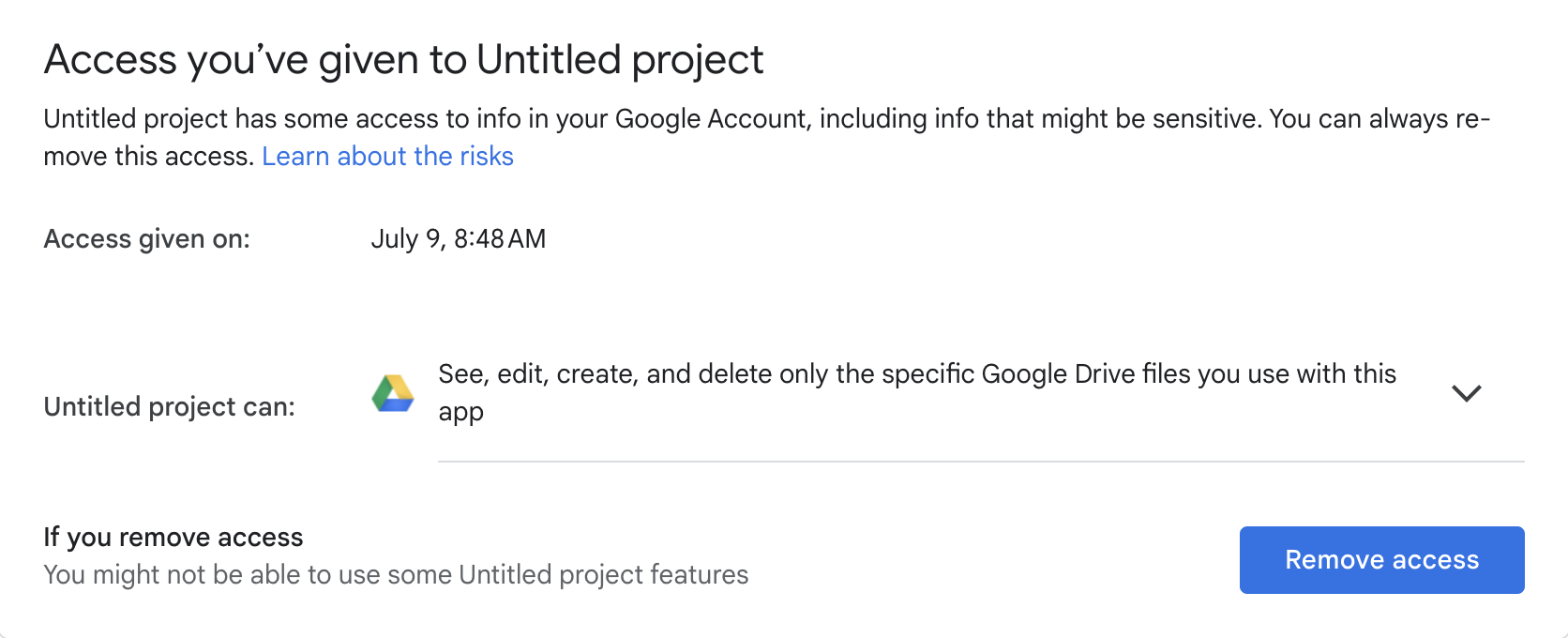
Then you can review permissions for each of the apps and decide whether to revoke them:
Review Triggers
Triggers enable scripts to execute without your direct involvement, such as at specific times. However, this feature presents a risk: if someone else can modify the script, they can make it do anything within the script’s authorization scopes. You can review all your account’s triggers here and make necessary adjustments or deletions.
While removing triggers doesn’t change the scopes, it reduces the risk that the scope can be misused.
Going Through Scripts Manually
The script.google.com portal displays all the scripts/projects you’ve created or have been given access to. This method is a bit more tedious but helpful for in-depth reviews or identifying specific scripts.
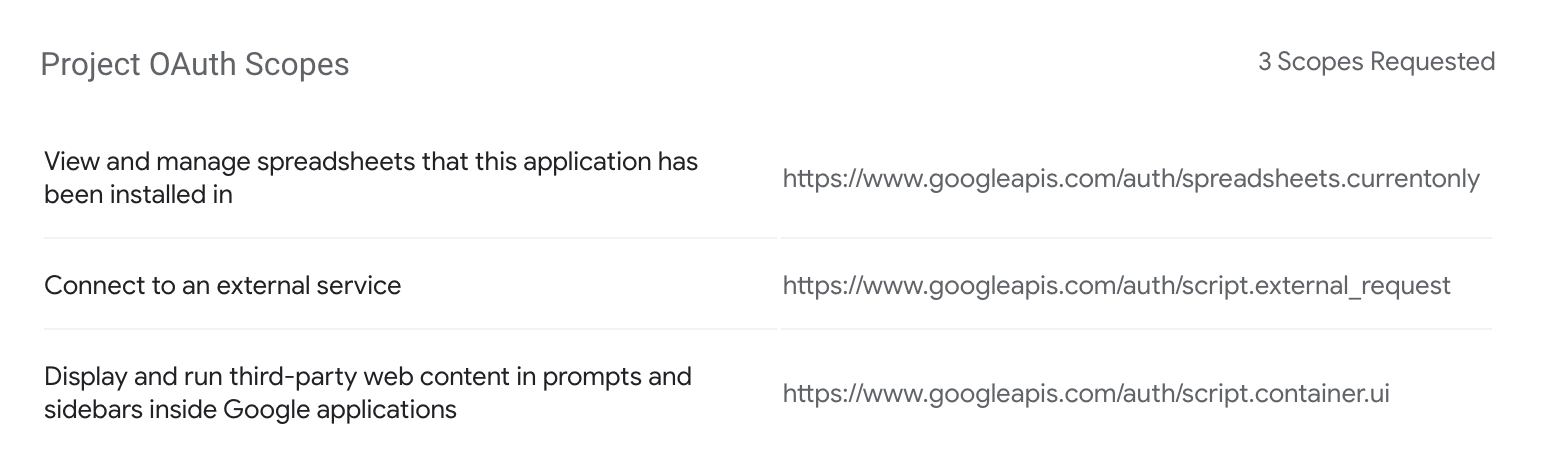
Each Apps Script project has an overview section where you can see scopes requested by the scripts. However, there you cannot see whether you granted those permissions. For that you need to go to either Security Checkup or Third-party apps & services in the account settings (more on that below).
Another place where you might be able to see permissions is the manifest file. However, by default it is hidden and doesn’t contain the permissions. More on the manifest file here.
Review Script Executions
This section allows you to see recent script executions under your account, access the relevant project, view logs, and more. This can be useful for a more in-depth review.
Remember, scopes are a vital aspect of your data security. While Google provides several tools for auditing and revoking them, it’s ultimately up to you to use them wisely and minimize the risk of breaches. Stay vigilant, regularly review your permissions, and remain proactive in maintaining your data’s safety.